The ever-growing threats from cyberspace are increasingly targeting operational technology (OT) in various automation and control solutions. The increased connectivity and technology standardization of these systems enables hackers to carry out attacks that are easier to execute, require fewer resources and are more comprehensive than ever before. After a thorough analysis of the risks and vulnerabilities in your operating environment and a requirement analysis, we provide you with a catalog of effective remedy measures and prioritize those areas or processes where action is most urgently needed.
OT Security Health Check
We analyze the security state of your systems and make you more resilient against cyberattacks
Do you want to increase your resilience against cyber attacks?
For example, the impact of new interfaces can be evaluated, the effectiveness of typical processes such as change, patch and vulnerability management or general technical weaknesses can be identified and taken into account as part of a risk assessment. In this way, we support you in reducing your security risks to an acceptable level in the long term.
Secure Industry 4.0
Cyber security is a central component of modern production systems. We independently check whether your OT systems and protection concepts meet current security standards – for a reliable, digital future.
Recognize attack surfaces
Many OT components have no cyber security functions. An OT penetration test checks the effectiveness of compensatory measures, such as controlled access.
Uncovering vulnerabilities
By identifying weaknesses and deriving measures from them, the stability and reliability of industrial and critical infrastructures are safeguarded.
Protect critical systems
Many OT systems form the infrastructural backbone of our society – for example in the energy and water supply or in industrial production. With our Health Check, you can make an active contribution to the security of these infrastructures.
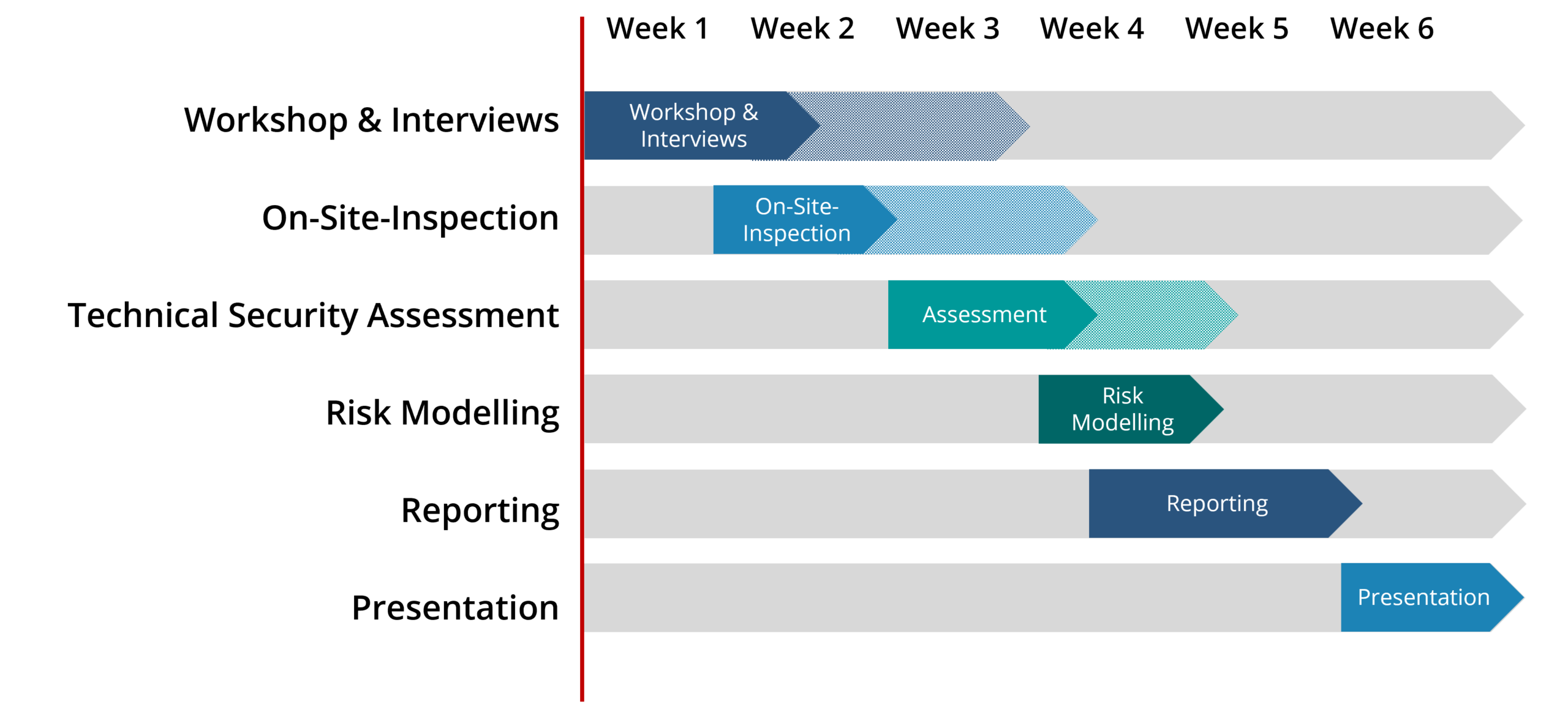
Individual steps of our OT security health check
Possible project plan
Is your company or product
protected against hacker attacks?
With our penetration tests, we help you to identify vulnerabilities in your IT and OT environment and develop appropriate countermeasures.

IEC 62443
Our OT Security Health Check is based on the internationally recognized IEC 62443 standard.
We identify risks and weak points in your operating environment and provide you with a prioritized catalog of measures. This allows you to see at a glance in which areas or processes there is a need for action in order to meet the requirements of IEC 62443.
This not only makes it easier for you to comply with regulatory requirements, but also keeps your security architecture permanently up to date with the latest technology.
Through clearly defined security objectives, measures and processes, we help you to reduce cyber risks to an acceptable and controllable level.